Slashy handles your email, calendar, and contacts. Security is the foundation, not a feature.Documentation Index
Fetch the complete documentation index at: https://help.slashy.com/llms.txt
Use this file to discover all available pages before exploring further.
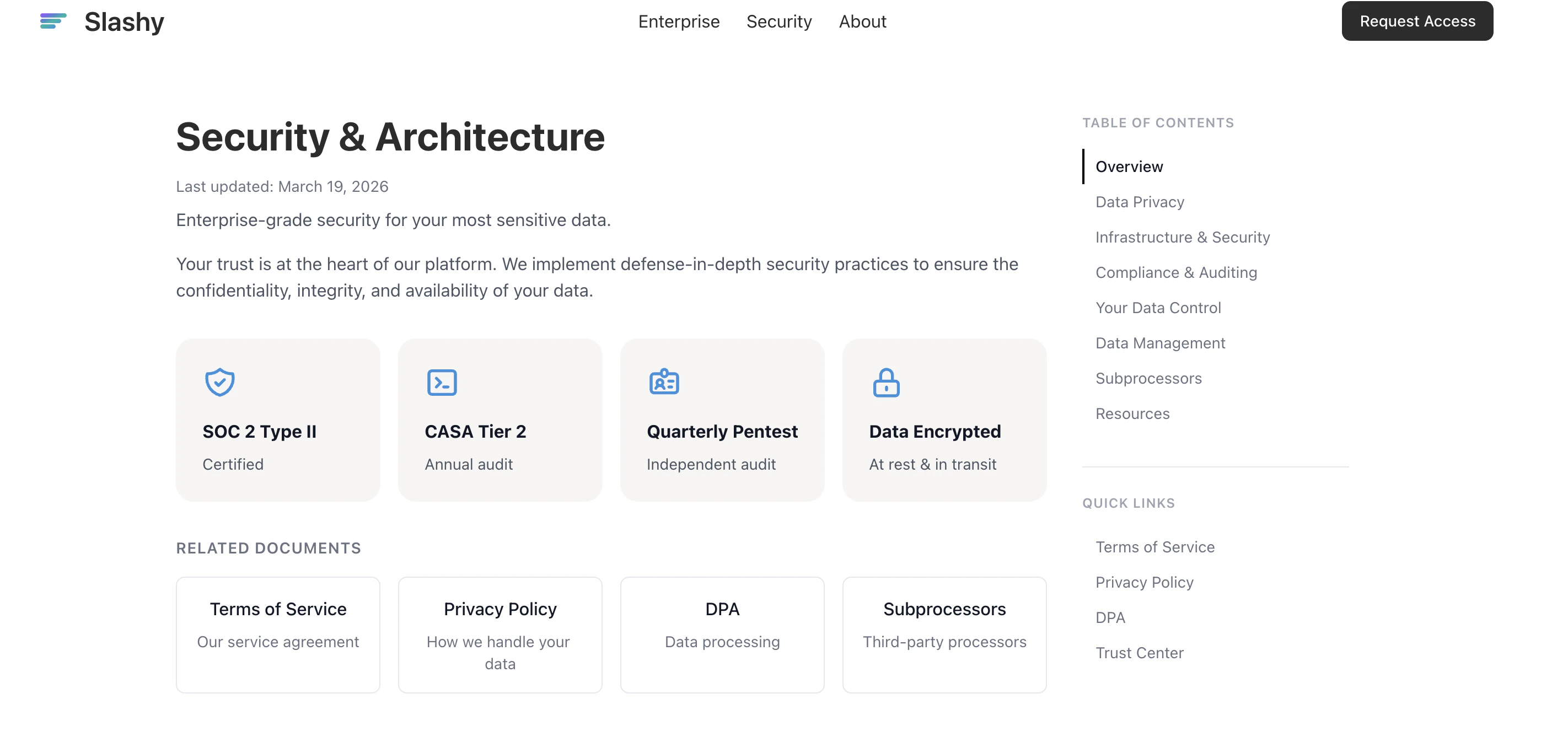
Certifications
| Certification | Status |
|---|---|
| SOC 2 Type II | Audited annually |
| CASA Tier 2 | Google Cloud Application Security Assessment — passed |
| Penetration Testing | Quarterly, independent third-party firm |
| Encryption | AES-256 at rest, TLS 1.2+ in transit |
AI and Your Data
Does the AI train on my emails? No. Every AI provider is contractually bound to a zero-training agreement. Your data is processed to generate a response and then discarded.| AI Provider | Used For | Trains on Your Data? |
|---|---|---|
| Anthropic (Claude) | Drafts, agent, automations | No — contractually prohibited |
| OpenAI | Drafts, editing, autocomplete | No — contractually prohibited |
| Google (Gemini) | Categorization, search | No — contractually prohibited |
| Groq | Fast inference tasks | No — contractually prohibited |
Prompt Injection Protection
Malicious emails can contain hidden instructions to trick AI assistants. Slashy sanitizes and isolates incoming email content from system instructions before it reaches any model. The agent cannot take unauthorized actions and flags suspicious content.What Data Slashy Stores
- Email metadata and content — cached for fast access
- Calendar events — synced from Google Calendar
- Agent conversations — your AI sidebar chat history
- Memories — preferences, contacts, writing style
- Automation logs — what ran and when
- Usage analytics — anonymous, via PostHog
OAuth Access Model
- Slashy never sees or stores your Google password
- You grant specific permissions you can revoke anytime at myaccount.google.com/permissions
- OAuth tokens stored encrypted, refreshed automatically
- Same model applies to optional integrations (Zoom, Granola)
Data Deletion Timeline
| Step | Timing | What Happens |
|---|---|---|
| Revoke access | Immediate | OAuth tokens invalidated. No more email/calendar access. |
| Hard delete | Within 24 hours | All data permanently deleted from production. |
| Backup purge | Within 7 days | Data removed from encrypted backups. |
Trust at a Glance
SOC 2 Type II
Audited annually by an independent firm
Zero-Training Guarantee
No AI provider trains on your data
AES-256 Encryption
Data encrypted at rest and in transit
Common Security Questions
Where is my data stored?
Where is my data stored?
Encrypted servers in the United States, hosted on AWS with SOC 2 compliance. All data encrypted with AES-256 at rest and TLS 1.2+ in transit.
Do Slashy employees read my emails?
Do Slashy employees read my emails?
No. Employee access to production data is restricted, logged, and auditable. No one reads your email unless you explicitly share it for debugging.
Can I get your SOC 2 report?
Can I get your SOC 2 report?
Yes. Visit slashy.com/security to request the full report, pen test summary, and compliance documents.
Do you have a bug bounty program?
Do you have a bug bounty program?
Yes. Email founders@slashy.com with details. We respond within 24 hours.
Is Slashy safe for my company's data?
Is Slashy safe for my company's data?
Yes. Slashy is built for professionals handling sensitive email. SOC 2 Type II audited, quarterly pen-tested, and all AI providers contractually prohibited from training on your data. Many VC firms, startups, and enterprise teams use Slashy for confidential communications.
What happens if Slashy is breached?
What happens if Slashy is breached?
Slashy maintains an incident response plan tested quarterly. In the event of a breach, affected users are notified within 72 hours per GDPR requirements. Encrypted data at rest means raw email content is not exposed even if infrastructure is compromised.
Can I use Slashy with a Google Workspace admin policy?
Can I use Slashy with a Google Workspace admin policy?
Yes. Slashy uses standard Google OAuth 2.0 with scoped permissions. Your Workspace admin can approve Slashy as a trusted app and control which users can connect. See Connecting Gmail for permission details.
Related Articles
AI Privacy
How AI providers handle your data
Data Storage
What Slashy stores and your controls
Connecting Gmail
OAuth permissions and what Slashy accesses
Subprocessors
Full list of infrastructure providers